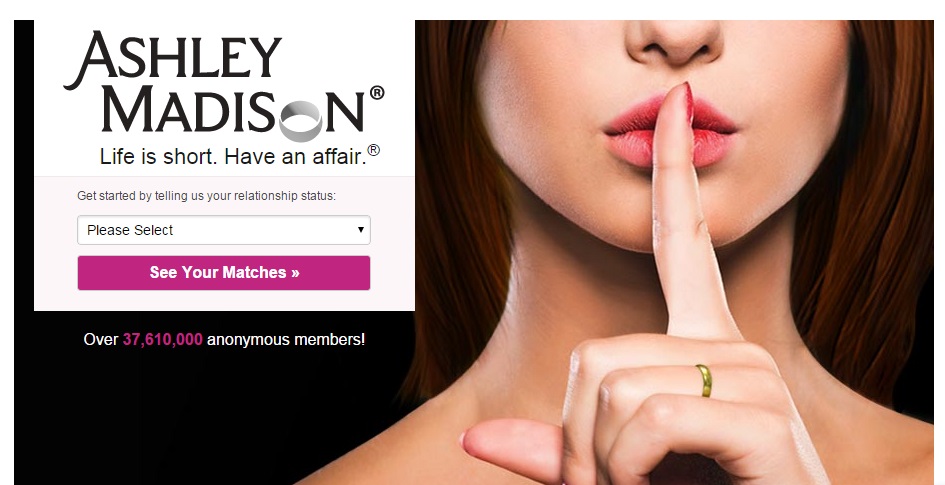
Some secrets are more valuable than others. And some secrets are more valuable TO others. In perhaps the most predictable extortion hack ever, cheating website Ashley Madison has confirmed to Brian Krebs that some of its data has been stolen. It now appears that tens of millions of people are at risk of being exposed. As you’ve already deduced, Ashley Madison users are not really all that worried about having the credit card numbers stolen and used for fraud.
According to Krebs, the hackers — who go by the name The Impact Team — say they will slowly dribble out data from the site until its owners take the cheating site, and companion site “Established Men,” offline.
“Avid Life Media has been instructed to take Ashley Madison and Established Men offline permanently in all forms, or we will release all customer records, including profiles with all the customers’ secret sexual fantasies and matching credit card transactions, real names and addresses, and employee documents and emails,” Krebs quotes the hackers from a post they left behind.
This is hacking 2.0. It’s not about the data, it’s about the context. Using stolen data, like credit cards, to get money is hard work. Extorting someone who has more to lose than money is a lot more profitable.
When Sony was hit by a combination hack / extortion plot in December, I described this new era of hacking. Sony corporate emails were stolen by hackers, who then embarrassed the heck out of the firm. Execs said inappropriate, even racist, things. Actresses were insulted and underpaid. It all reminded me of a smaller, but no less scary, incident several years ago involving a government contractor named HB Gary, which had Anonymous similarly terrorized.
Criminals don’t have to steal financial information to make money hacking. They just have to steal any data that’s valuable to anyone.
Making matters worse for corporate security teams is this reality: In recent years, they’ve all invested heavily in protecting financial data, spending money fortifying the most valuable data. Credit cards, yes. Email servers, maybe not. Slowly, this will change. But right now, every executive at every firm in the country should be hard at work doing an honest assessment about what their valuable data really is. Then, they need to invest wisely in protecting data that might seem inconsequential if stolen in one context, but a disaster of stolen in another. Because every company will have to plan for ransom and extortion requests now.
It’s hard to understand why Ashley Madion’s owners didn’t see this coming…particularly when AdultFriendFinder.com was hacked two months ago. But that is how these things go.
The next question in this incident is: How will Avid Life Media get out of this mess? One possibility is paying a ransom. A few months ago, I started researching ransom and what I’ll call “data kidnapping” after I’d gotten a whiff this was going on. The raging success of malware called cryptolocker, which forced victims to pay a few hundred dollars’ ransom to unscramble their data, certainly proved extortion demands can work. Cryptolocker made $27 million just in its first two months, from both home users and small organizations.
When I talked to Lisa Sotto, a cyberlaw expert at Hunton & Williams, about this recently, she said she believed things were only going to get worse.
“That’s exactly how I see it going. Companies and individuals paying, because they potentially have no choice,” Sotto said to me. In fact, ransoms are already common, she said. “I do not believe there is a heck of a lot of negotiation involved…They are not asking for exorbitant amounts, so for the most part, what I hear is people are paying.”
In February, a blog post by Christopher Arehart made me even more convinced that ransom and extortion are hacking 2.0. Arehard is is the global product manager for crime, kidnap/ransom and extortion, and workplace violence expense insurance for the Chubb Group of Insurance Companies. In his post, he warned companies that cyber-insurance policies often don’t cover extortion situations.
“Cyber liability insurance policies may help companies deal with first-party cleanup costs, the cost of privacy notifications and lawsuit expenses, but these policies may only provide limited assistance with extortion threats. Extortion threats should be investigated and handled by professionals and small businesses need to know where to turn for assistance,” he wrote.
He then wrote that many businesses should consider adding the same kind of insurance that multinational companies purchase when they must send employees into dangerous parts of the world.
“A kidnap and ransom policy — technically a kidnap, ransom and extortion (KRE) policy — responds when an extortion threat has been made against a company, before there has been any data breach,” he wrote.
I tried to ask Arehart and Chubb about incidents involving extortion or “data kidnapping,” but the firm just pointed me back to his blog.
“Although some criminals eventually back down and do not follow through with their extortion threats, some threats do get carried out and these incidents can often be expensive. The tools available to criminals are vast and they have the power of the Internet behind them. Businesses, especially small businesses, need access to security consultants to help them manage these threats. A KRE policy would provide small businesses with access to those professionals.”
In other words, kidnapping and ransom policies aren’t just for dealing with employees who might run into the Mexican drug cartel any more.
They are for anyone who has data that might be valuable to someone, in some future context. Secrets are almost always valuable to someone.