Ponemon Institute is pleased to present the findings of the 2016 Cost of Insider Threats study sponsored by Dtex. The purpose of this benchmark study is to understand the direct and indirect costs that result from insider threats. In the context of this research, insider threats are defined as:
- A careless or negligent employee or contractor,
- A criminal or malicious insider or
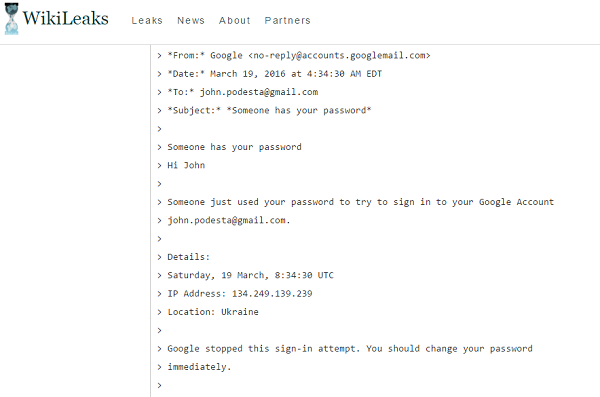
- A credential thief.
We interviewed 280 IT and IT security practitioners in 54 organizations from April to July 2016. Each organization experienced one or more material events caused by an insider. These organizations experienced a total of 874 insider incidents over the past 12 months. Our targeted organizations were business organizations with a global headcount of 1,000 or more employees located throughout the United States.
Imposter risk is the most costly
The cost ranges significantly based on the type of incident. If it involves a negligent employee or contractor, the incident can average $206,933. The average cost more than doubles if the incident involves an imposter or thief who steals credentials ($493,093). Criminal and malicious insiders cost the organizations represented in this research an average of $347,130. The activities that drive costs are: monitoring & surveillance, investigation, escalation, incident response, containment, ex-post analysis and remediation.
The negligent insider is the root cause of most incidents
Most incidents in this research were caused by insider negligence. Specifically, the careless employee or contractor was the root cause of almost 600 (598) of the 874 incidents reported. The most expensive incidents, due to imposters stealing credentials, were the least reported and totaled 85 incidents.
Organizational size and industry affects the cost per incident
The cost of incidents varies according to organizational size. Large organizations with a headcount of more than 75,000 spent an average of $7.8 million to resolve the incident. To deal with the consequences of an insider incident, organizations with a headcount between 1,000 and 5,000 spent an average of $2 million. Financial services, retail, industrial and manufacturing spent an average of $5 million.
User behavior analytics combined with other tools reduce the total cost
Using incremental analysis, we recalculated the total cost of insider-related incidents under the condition that a given tool or activity is deployed across the enterprise. Companies that deploy user behavior analytics (UBA) realized an average cost reduction of $1.1 million. The use of threat intelligence systems resulted in an $0.8 million average cost reduction. Similarly, the deployment of data loss prevention (DLP) tools resulted in an average cost reduction of $0.7 million. Companies that deploy user behavior analytics in combination with threat intelligence, employee monitoring and data loss prevention have an average total cost of $2.8 million, which is $1.5 million lower than the overall average.
Click here to read the rest of the study